I’ve been thinking of some use cases where it could be useful to be able to send secret messages on-chain (and off-chain) in such a way that only the intended recipient could decrypt the message.
Cryptography isn’t exactly my area of expertise but I’m interested in the possibilities cryptography can offer us so I dipped my toes in and made a simple proof-of-concept implementation of sending encrypted on-chain messages using the Sodium cryptography library. This PoC allows you to send an encrypted message to a NoM address that can only be decrypted by the address’ owner.
Since NoM uses the Ed25519 signature scheme we can convert a keypair into X25519 and then encrypt a message for a public key so that the message can only be decrypted with the corresponding private key.
This allows us to send an encrypted message to a recipient who can decrypt the message using their keypair.
The modified CLI wallet can be found here: GitHub - vilkris4/znn_cli_dart at secret_messages
The wallet requires the libsodium library to work.
On Windows it’s easiest to download the pre-built DLL and copy it to the CLI’s folder: Installation | Libsodium documentation (I used libsodium-1.0.18-stable-msvc.zip)
On Mac you can use Homebrew to install libsodium: libsodium — Homebrew Formulae
Example
I added two commands to the wallet: sendEncryptedMessage and decryptMessage
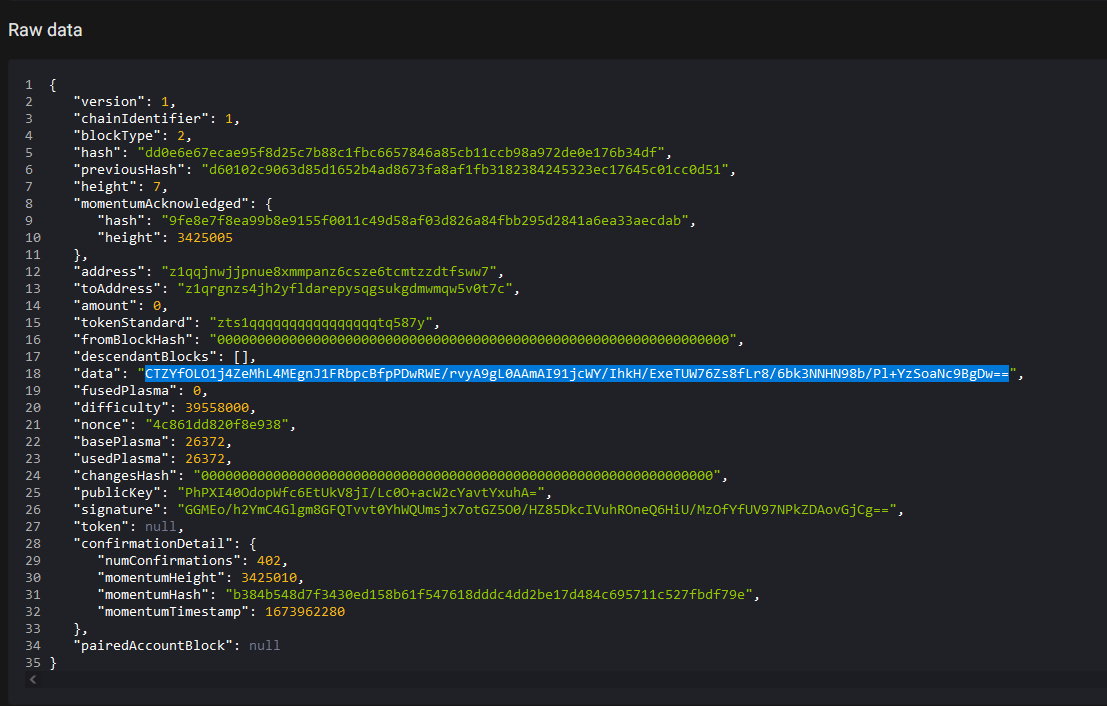
An example of sending an encrypted message to address z1qrgnzs4jh2yfldarepysqgsukgdmwmqw5v0t7c:
.\znn-cli.exe sendEncryptedMessage z1qrgnzs4jh2yfldarepysqgsukgdmwmqw5v0t7c “This is top secret information.”
An example of the recipient decrypting the message:
.\znn-cli.exe decryptMessage CTZYfOLO1j4ZeMhL4MEgnJ1FRbpcBfpPDwRWE/rvyA9gL0AAmAI91jcWY/IhkH/ExeTUW76Zs8fLr8/6bk3NNHN98b/Pl+YzSoaNc9BgDw==
Output:
This is top secret information.
In this example the recipient has to get the encrypted message from the explorer by viewing the transaction that has the message and then copying the contents of the data property into the terminal:
It’s worth noting that these encrypted messages can be sent off-chain as well but for this PoC I wanted to make it on-chain.
If someone wants to try it out, DM me your address and I can send you an encrypted message.