This guide will explain how to configure your network to adequately protect your personal internal LAN when running a Public Node. To commence this guide you need to have:
- Deployed ZNND to a Raspberry Pi or local host
- Set up a local firewall on the host
These 2 steps allow you to utilize the ZNN Node internally on your LAN. To make it Public (i.e. allow anyone on the internet to be able to access it) you need to port forward or NAT your nodes internal LAN IP to your Public facing ISP IP.
This comes with some inherit risk, as you are exposing something in your internal LAN (trusted network) to the internet (untrusted), so there are some strategies you can follow for added protection:
- Only port forwarding on the specific ZNN ports
- Configuring the host in its own VLAN segregated from your internal LAN
- Configuring a Gateway firewall (on your router or similar device)
We will go through the process of setting this up in the Unifi ecosystem, as at the time of writing this guide the current release is Network 7.0.23.
-
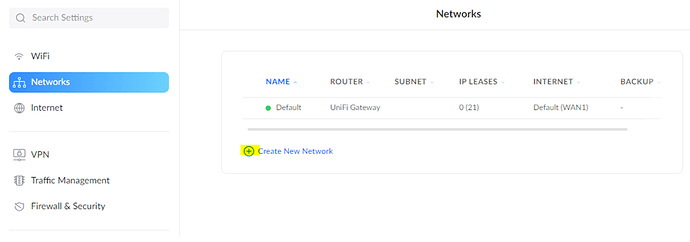
Browse to Settings>Networks>Create New Network
-
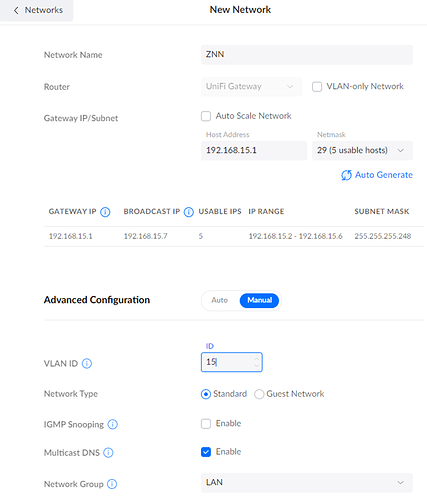
Give the network a custom Name, and select a subnet that differs from your other networks.
-
Configure the netmask for your desired subnet size.
-
Choose a VLAN ID and leave all other settings as default
-
At this point you would need to reconfigure your hosts IP address to reside within this new VLAN, and re-patch on your switch if necessary. We now have the ZNN node residing in its own VLAN, but it can still successfully communicate with the rest of your internal LAN – the next step is to prevent this from happening with firewall rules.
-
Browse to Settings>Firewall & Security and under Firewall Rules select LAN and Create New Rule.
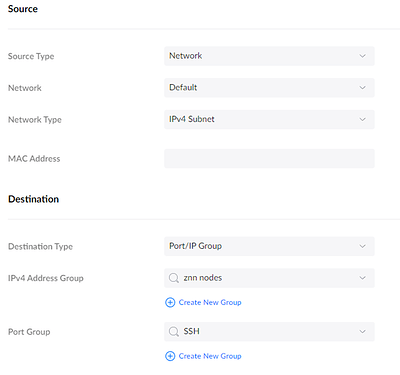
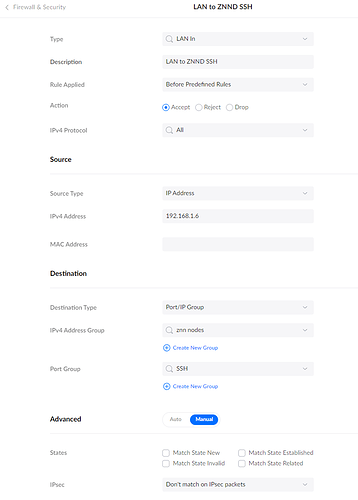
Rule 1 will allow your Internal LAN to reach the host via SSH only:
Type: LAN in
Description: Anything you want
RuleApplied: Before Predefined Rules
Action: Accept
Source: Configure your internal LAN or a specific IP for your home PC here
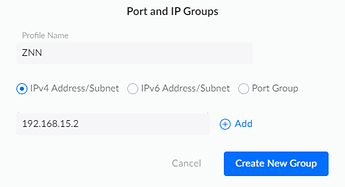
Destination: Select Port/IP Group and create an IP group that contains your host
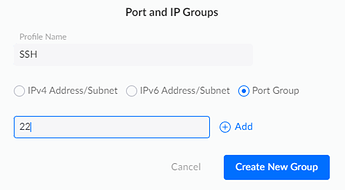
Destination: Select Create New Group again and Choose Port Group, enter a name and add port 22 (for SSH)
- The final rule should look like the above image (press Apply Changes)
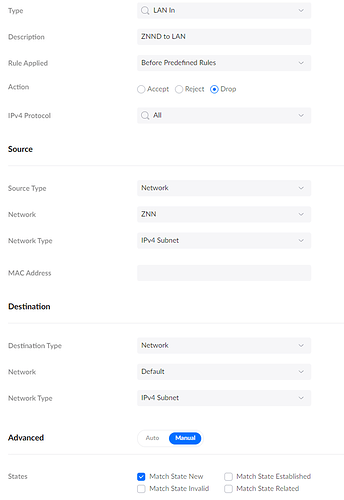
Rule 2 will block access to your Internal LAN from the new ZNN VLAN:
Type: LAN in
Description: Anything you want
RuleApplied: Before Predefined Rules
Action: Drop
Source: Select your ZNN Network VLAN here
Destination: Select your Default LAN network here
Advanced: Manual
States: Match State New (only select this one)
-
Now that the ZNND Node is isolated from your internal network, we need to create firewall rules that govern its interaction with the Internet.
-
Browse to Settings>Firewall & Security and under Firewall Rules select Internet and Create New Rule.
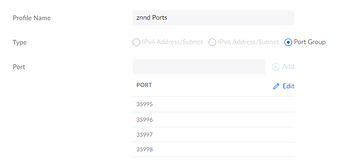
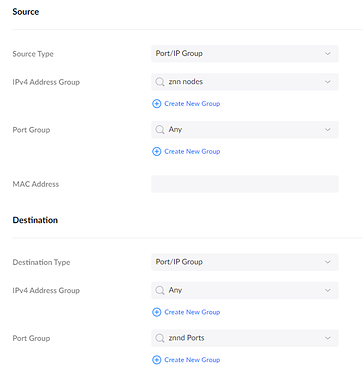
Rule 3 will allow the node to talk to the internet over specified ports:
Type: Internet Out
Description: Anything you want
RuleApplied: Before Predefined Rules
Action: Accept
Source: Select the ZNN IP group you created earlier
Destination: Port/IP Group and Create a new port group and add ports 35995, 35996, 35997, 35998
Advanced: Auto
- Press Apply Changes and create another new rule
Rule 4 will drop all other activity from the Node to the Internet:
Type: Internet Out
Description: Anything you want
Rule Applied: Before Predefined Rules
Action: Drop
Source: Select the ZNN IP group you created earlier
Destination: Any Any
Advanced: Manual
States: Match State New (only select this one)
- Finally, we need to configure Port Forwarding so that external connections to your Public IP by Syrius wallets are sent to your internal IP address for the Node. Browse to Settings>Firewall & Security>Port Forwarding>Create New Port Forwarding
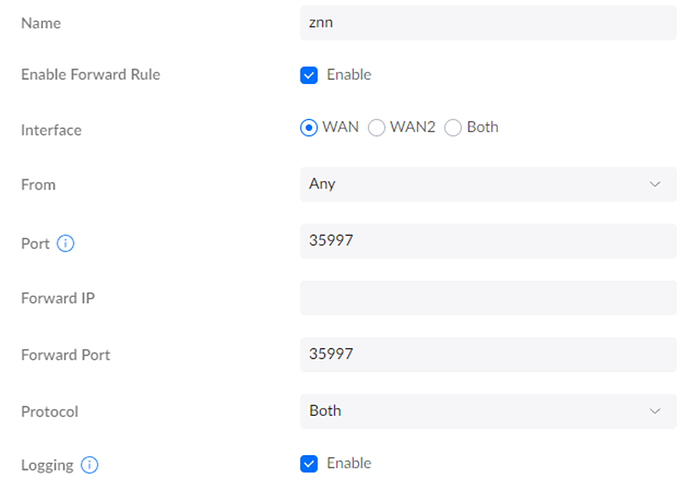
Port Forward 1
Name: ZNN
Enable Forward Rule: Ticked
Interface: WAN
From: Any
Port: 35997
Forward IP: The IP of your Node
Forward Port: 35997
Protocol: Both
Port Forward 2
-
Repeat the process for port 35998.
- And now you’re done, you can connect to your node via the Public IP that you have from your ISP. On Unifi this can be found on the dashboard as below: